Ready to protect your online world with rock-solid security? You don’t need to be a tech expert or spend hours setting up complicated systems.
With Authyo, launching strong authentication is as easy as 1-2-3. Imagine securing your accounts using SMS, email, and WhatsApp—all in one smooth process. You’ll discover how to set up powerful, three-factor authentication that keeps your data safe from hackers and threats.
Stick with us, and you’ll have your defenses up in no time, giving you peace of mind and control over your digital life. Let’s dive into the simple steps that make this possible.
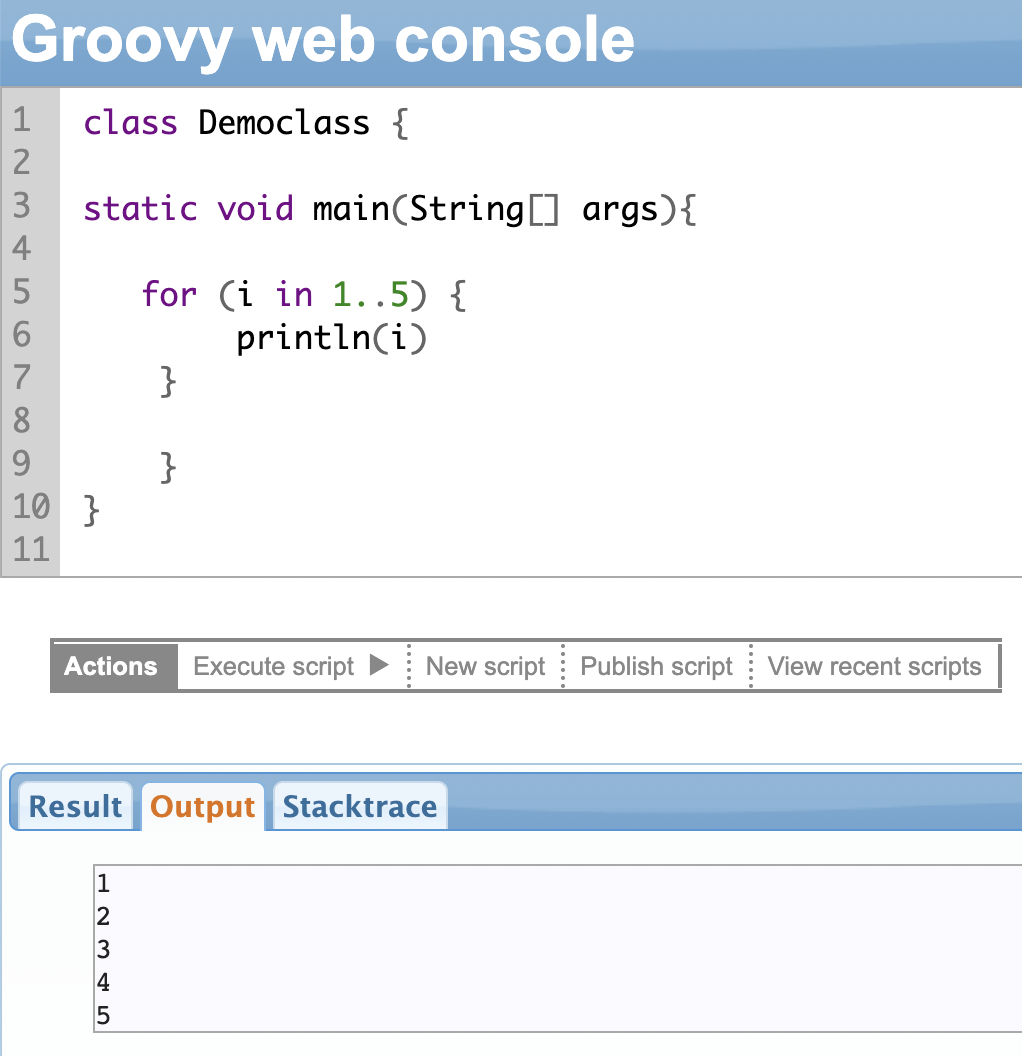
Credit: exalate.com
Introduction To Rock-solid Authentication
Rock-solid authentication ensures only the right users access your systems. It uses strong methods to confirm identity and keep accounts safe.
Security today demands more than just a password. Threats grow daily, making simple login methods risky. Strong authentication adds layers of protection.
This section explains how three-factor authentication works and why fast, secure login matters now more than ever.
Understanding The Concept Of Three-factor Authentication
Three-factor authentication uses three types of credentials to verify a user’s identity. These are:
- Something You Know (Knowledge Factor): Information only the user knows, like passwords or PINs.
- Something You Have (Possession Factor): A physical device the user carries, such as a smartphone or security token.
- Something You Are (Biometric Factor): Unique body traits like fingerprints, facial scans, or voice recognition.
Example of use:
- Enter your password.
- Scan a QR code on your phone to generate a temporary code.
- Verify your identity with a fingerprint scan.
Combining these factors greatly reduces the risk of unauthorized access. If one factor is stolen or guessed, the others still protect your account.
Why Secure Fast Authentication Matters In Today’s Digital World
Speed and security must go hand in hand. Users want quick access but expect strong protection.
Here are reasons why secure, fast authentication is crucial:
- Protects sensitive data from hackers and unauthorized users.
- Stops common attacks like stolen passwords or fake biometric data.
- Supports high-security environments such as banking, healthcare, and corporate systems.
- Improves user experience by reducing login delays without lowering security.
Tools like Authyo enable smooth authentication over SMS, Email, and WhatsApp. This helps businesses secure their platforms while keeping user access simple and fast.
The Three Essential Authentication Factors Explained
Authentication relies on three key factors to verify a user’s identity. Each factor offers a unique layer of security. Using all three together creates a strong defense against unauthorized access. These factors are something you know, something you have, and something you are.
This method ensures that even if one factor is compromised, the others still protect your account. Let’s break down these essential authentication factors in simple terms.
Something You Know: Leveraging Knowledge-based Credentials
This factor is based on information only the user should remember. It includes passwords, PINs, or answers to security questions. These credentials are the first line of defense.
To keep this factor secure:
- Choose strong passwords with letters, numbers, and symbols.
- Change passwords regularly.
- Avoid common or easy-to-guess answers for security questions.
Something You Have: Utilizing Physical Possession For Security
This factor requires a physical item the user holds. Examples include:
- A smartphone with an authenticator app.
- A security token or hardware key.
- A device that can receive SMS or Email codes.
The user proves identity by showing possession of this item. For example, scanning a QR code to generate a temporary code on their phone.
Something You Are: The Power Of Biometric Verification
This factor uses unique biological traits. It verifies identity through:
- Fingerprint scans
- Facial recognition
- Voice recognition
- Iris scans
Biometrics are hard to fake and add a strong security layer. Scanning a fingerprint to confirm identity is a common use case.
| Factor | Example | Purpose |
|---|---|---|
| Something You Know | Password, PIN | Confirm knowledge only the user has |
| Something You Have | Smartphone, Security Token | Confirm physical possession |
| Something You Are | Fingerprint, Face Scan | Confirm unique biological traits |
Step 1: Setting Up Knowledge-based Authentication
Knowledge-Based Authentication forms the first layer of robust security. It relies on information only the user knows, such as passwords or PINs. This method is simple but effective at blocking unauthorized access. Setting it up correctly ensures a strong foundation for multi-factor authentication.
Using Authyo, you can easily implement this step via SMS, Email, or WhatsApp, making user verification seamless and secure.
Creating Strong Passwords And Pins For Maximum Security
Strong passwords and PINs are vital. They act as the first defense against attackers.
- Use at least 8 characters combining letters, numbers, and symbols.
- Avoid common words or simple patterns like “1234” or “password”.
- Change passwords regularly and never reuse them across sites.
- Use a PIN with at least 6 digits for added protection.
Authyo supports enforcing strong password policies automatically.
How Knowledge Factors Prevent Unauthorized Access
Knowledge factors stop intruders by requiring secret information only users know. Without the correct password or PIN, access is denied.
This method works well because:
- It verifies identity before any other authentication step.
- It reduces risks from lost or stolen physical devices.
- It is easy to implement and understand for users.
Combining knowledge factors with possession and biometric factors creates a strong multi-factor system.
| Authentication Factor | Example | Security Role |
|---|---|---|
| Knowledge Factor | Password, PIN | Proves user knows secret information |
| Possession Factor | Smartphone, Authenticator App | Confirms user has a trusted device |
| Biometric Factor | Fingerprint, Face Scan | Verifies unique physical traits |
Start with strong knowledge factors using Authyo’s easy setup. Protect your system from the start.
Step 2: Integrating Possession-based Authentication
Possession-based authentication adds a crucial layer of security. It requires users to prove they have a physical device. This method strengthens identity verification beyond just passwords.
Using Authyo, integrating possession factors like security tokens or authenticator apps becomes simple and effective. It stops unauthorized access even if passwords are stolen.
Using Security Tokens And Authenticator Apps Effectively
Security tokens and authenticator apps generate temporary codes users enter to confirm their identity. These codes change frequently, making it hard for attackers to reuse them.
- Security Tokens: Small hardware devices that display a time-based code.
- Authenticator Apps: Apps like Google Authenticator or Authyo app that generate codes on smartphones.
To use these tools effectively:
- Register the token or app with your system.
- Prompt users to enter the generated code during login.
- Verify the code on your server for authentication.
This process ensures only users with the physical device can log in, preventing unauthorized access.
Benefits Of Physical Devices In Strengthening Authentication
Physical devices offer several security benefits that improve overall authentication:
| Benefit | Explanation |
|---|---|
| Increased Security | Requires possession of a device, making remote hacks difficult. |
| Protection Against Password Theft | Even stolen passwords cannot grant access without the device. |
| Easy User Experience | Users only need to enter a short code from their device. |
| Compatibility | Works with many platforms and integrates well with Authyo. |
Integrating possession-based authentication with Authyo increases your system’s defense. It reduces risks from stolen credentials and boosts user trust.
Step 3: Implementing Biometric Authentication Seamlessly
Biometric authentication adds a vital layer of security by using unique biological traits. It ensures only authorized users gain access. Integrating biometrics with Authyo’s multi-factor system boosts both safety and convenience. This step focuses on fingerprint, facial, and voice recognition technologies. Each method offers a different way to verify identity without extra passwords or tokens.
Fingerprint, Facial, And Voice Recognition Technologies
These biometric methods rely on physical or behavioral traits. They are easy to use and hard to fake. Here’s a brief overview:
| Technology | How It Works | Common Use Cases |
|---|---|---|
| Fingerprint Recognition | Scans unique ridge patterns on fingertips. | Unlocking devices, app access, secure payments. |
| Facial Recognition | Analyzes facial features and geometry. | Device login, identity verification, access control. |
| Voice Recognition | Identifies speaker by voice tone and patterns. | Phone banking, virtual assistants, secure calls. |
Enhancing User Experience While Maintaining High Security
Biometric authentication with Authyo blends security and ease. Users avoid typing complex passwords repeatedly.
- Fast Access: Users authenticate with a simple touch or glance.
- Reduced Fraud: Biometrics are unique and difficult to duplicate.
- Multi-Factor Support: Combine biometrics with SMS or email verification for strong protection.
Seamless integration means no extra apps or hardware needed. Authyo supports various platforms and devices.
Implementing biometrics requires careful setup:
- Choose the biometric methods suitable for your users.
- Ensure devices support the chosen technology.
- Test the system thoroughly for accuracy and speed.
- Educate users about privacy and how their data is protected.
Secure and simple biometric authentication completes the strong Authyo framework.
Credit: www.prove.com
Pricing And Affordability Of Rock-solid Authentication Solutions
Choosing rock-solid authentication means balancing cost and security. Authentication solutions vary in price depending on tools and devices used. Understanding pricing helps businesses pick options that fit budgets while keeping data safe.
Cost Breakdown Of Authentication Tools And Devices
Authentication costs include hardware, software, and service fees. Here is a simple breakdown:
| Category | Examples | Typical Cost Range |
|---|---|---|
| Software | Authenticator apps, SMS/Email/WhatsApp OTP services | $0 – $10/user/month |
| Hardware Devices | Security tokens, biometric scanners | $20 – $100 per device |
| Setup & Maintenance | Integration, updates, support | Varies by provider |
Authyo offers affordable SMS, Email, and WhatsApp verification, reducing costs by using popular communication channels.
Evaluating Value Against Security Benefits
Security solutions protect against stolen passwords and device compromise. Strong authentication reduces risks of data breaches and fraud.
Consider these benefits:
- Prevents unauthorized access
- Protects sensitive information
- Builds user trust
- Supports compliance with regulations
Investing in solid authentication lowers long-term costs from security incidents. Affordable tools like Authyo provide strong multi-factor authentication without high fees.
Focus on solutions that combine ease of use, security, and cost-effectiveness to get the best value.
Pros And Cons Based On Real-world Usage
Three-factor authentication strengthens security by requiring three different credentials. Users must prove their identity through knowledge, possession, and biometrics. This method reduces risks from stolen passwords or lost devices.
Real-world experience shows clear benefits and some challenges. Understanding both helps decide if this method suits your needs.
Advantages Of Combining Three Authentication Factors
- Strong Security: Using three factors drastically lowers hacking chances.
- Protection Against Multiple Threats: Stolen passwords or lost tokens alone cannot grant access.
- Biometric Verification: Fingerprints or facial scans add a unique layer of identity.
- Reduced Fraud: Spoofing one factor won’t compromise the entire system.
- Flexible Use: Works with common tools like smartphones, authenticator apps, and biometrics.
| Authentication Factor | Example | Security Role |
|---|---|---|
| Something You Know | Password, PIN | Secret information only user knows |
| Something You Have | Smartphone, Security Token | Physical item to verify possession |
| Something You Are | Fingerprint, Facial Scan | Biometric data unique to user |
Potential Challenges And How To Overcome Them
User Convenience: Three steps can feel slow or complex for some users.
Simple guides and clear instructions ease the process. Authyo offers smooth integration with SMS, Email, and WhatsApp for easy factor delivery.
Device Dependence: Losing a phone or token blocks access.
- Set up backup methods like email verification.
- Use recovery codes stored safely offline.
Biometric Issues: Scanners sometimes fail or reject users.
- Allow alternative factors like PIN or token as backup.
- Keep biometric data encrypted and private.
Cost and Setup: More factors may increase setup time and expenses.
Choosing user-friendly tools like Authyo lowers complexity and cost. It supports multi-channel verification with simple API integration.
Ideal Users And Scenarios For Rock-solid Authentication
Rock-solid authentication suits users who need strong security and trust. It fits those who manage sensitive data or face many cyber threats. This method combines three factors: something you know, something you have, and something you are. This triple layer ensures the highest protection.
Different types of users and environments benefit from this approach. The right match depends on the risk level and data sensitivity. The next sections explain who gains the most and where three-factor authentication excels.
Who Benefits Most: Enterprises, High-security Environments, And Beyond
Large enterprises often handle valuable data and critical systems. Rock-solid authentication helps them avoid breaches and data leaks. These companies usually require strict access controls and compliance with regulations.
High-security environments like government agencies, banks, and healthcare providers need extra safety layers. Their work involves protecting personal, financial, or classified information. Three-factor authentication adds a strong shield.
Other ideal users include:
- Financial institutions securing online banking and transactions
- Cloud service providers protecting user accounts and data storage
- IT departments controlling access to critical infrastructure
- Businesses wanting to reduce fraud and identity theft risks
Use Cases Where Three-factor Authentication Makes The Biggest Impact
Three-factor authentication shines in scenarios where single or two-factor methods fail to stop attacks. Common use cases include:
| Use Case | Why Three-Factor Helps |
|---|---|
| Remote Workforce Access | Verifies identity beyond passwords and devices, blocking unauthorized logins |
| Financial Transactions | Prevents fraud by requiring a biometric check along with tokens and passwords |
| Healthcare Records Access | Ensures only authorized staff reach sensitive patient information |
| Admin Console Logins | Protects critical systems from insider threats and external hackers |
Each factor plays a role:
- Knowledge factor: Password or PIN only the user knows.
- Possession factor: A device or app generating temporary codes.
- Biometric factor: Fingerprint or facial scan confirming identity.
Authyo supports these factors via SMS, Email, and WhatsApp, making implementation simple and secure.
Conclusion: Launching Your Secure Fast Authentication Journey
Starting a strong authentication system is key to protecting your data and users. Authyo makes this process simple and fast. It combines SMS, Email, and WhatsApp for smooth verification. Secure access does not need to be complex. Follow clear steps to set up rock-solid security without delay.
Recap Of The Three Simple Steps To Rock-solid Security
These three steps build a strong shield around your system:
- Knowledge Factor: Users enter a password or PIN only they know.
- Possession Factor: Verification through a device like a phone with an authenticator app.
- Biometric Factor: Identity confirmed via fingerprint or facial recognition.
Together, these steps form three-factor authentication. This stops most attacks, such as stolen passwords or fake biometrics. The mix of factors blocks threats from different angles.
Next Steps To Implement And Maintain Strong Authentication
Follow these actions to keep your authentication strong and reliable:
- Integrate Authyo: Use SMS, Email, and WhatsApp channels to reach users easily.
- Test Regularly: Check each factor works well and data stays safe.
- Educate Users: Teach users why each step matters and how to use it.
- Update Security: Keep software and devices current to fight new threats.
Use this simple plan to launch a quick and safe authentication journey. Authyo supports all steps and helps maintain strong protection every day.
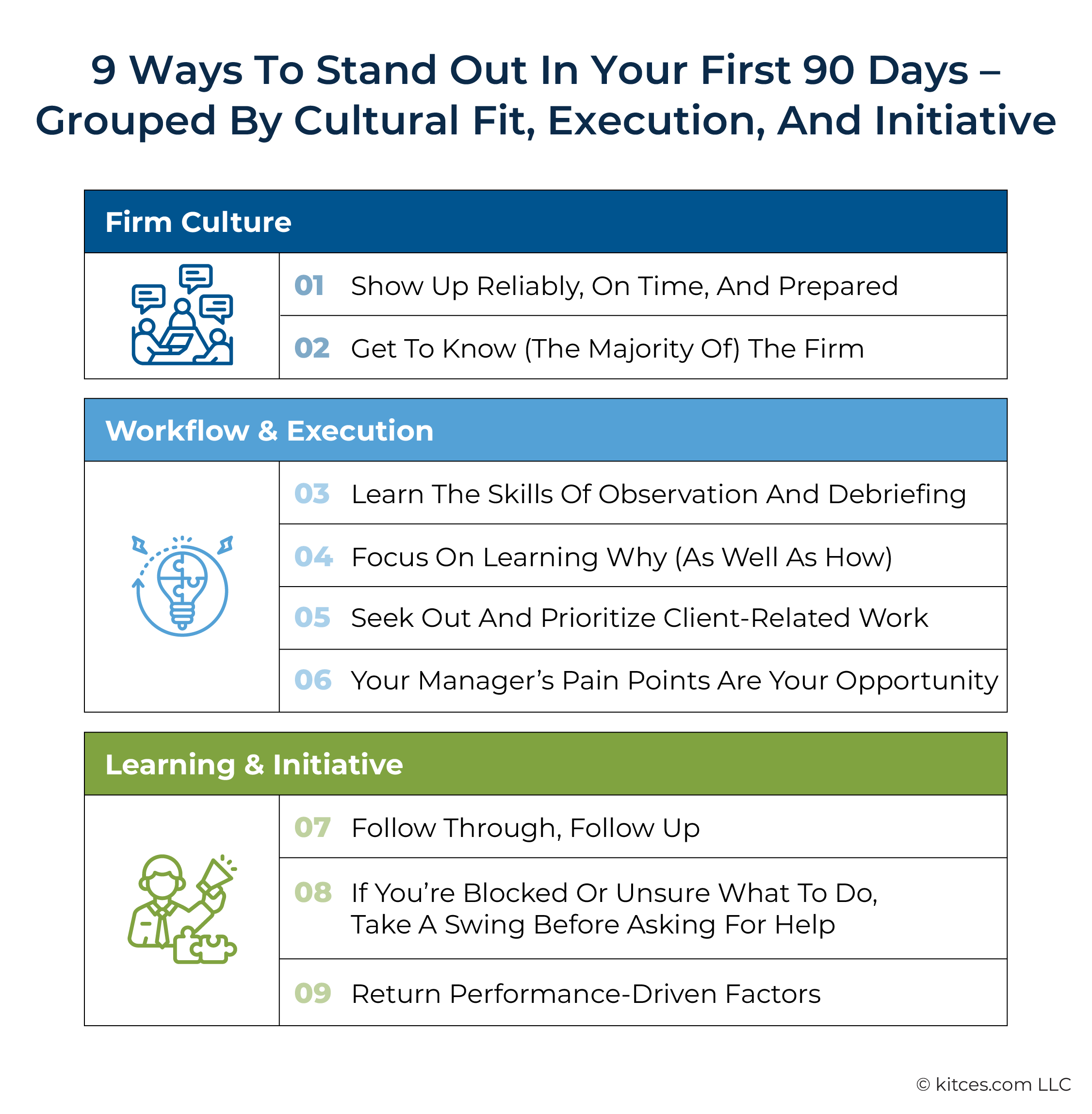
Credit: www.kitces.com
Frequently Asked Questions
What Is 3-step Authentication?
3-step authentication requires users to verify identity using three factors: something they know, have, and are. It enhances security by combining passwords, physical tokens or devices, and biometric data like fingerprints or facial recognition. This method protects accounts from unauthorized access and various cyber threats.
What Are The Three Components Of Authentication?
The three components of authentication are: something you know (password), something you have (security token), and something you are (biometrics).
What Are The Three Aspects Of A 3 Factor Authentication In Password Management Scheme?
The three aspects of 3-factor authentication are: something you know (password), something you have (security token), and something you are (biometrics).
What Are The 3 Simple Steps To Launch Authentication?
First, set up a strong password system. Next, enable an authenticator app or token. Finally, integrate biometric verification like fingerprint or facial recognition for added security.
Conclusion
Securing your accounts is easier than you think. Using Authyo, add three layers of protection. First, enter your password. Then, verify with your phone’s authenticator app. Finally, confirm identity using your fingerprint. This simple process keeps your data safe. It blocks hackers and reduces security risks.
Start today to protect your online presence. Strong authentication means peace of mind every day.